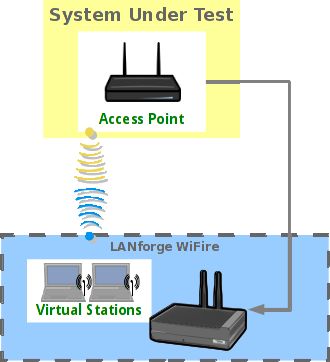
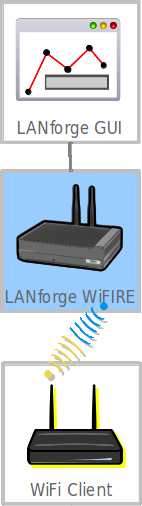
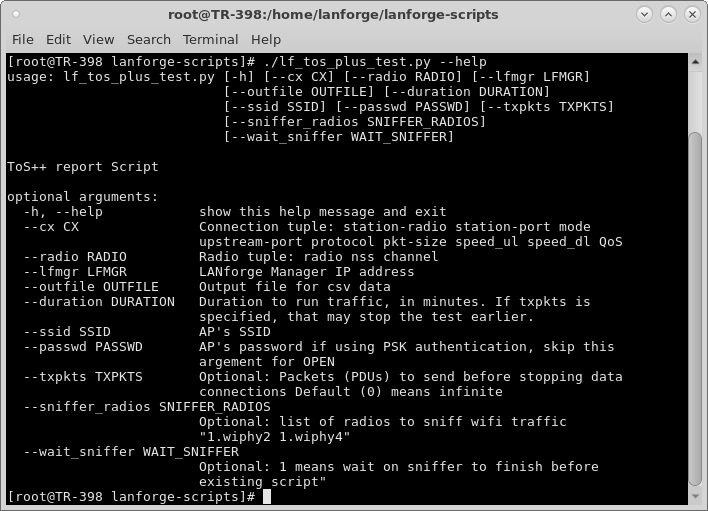
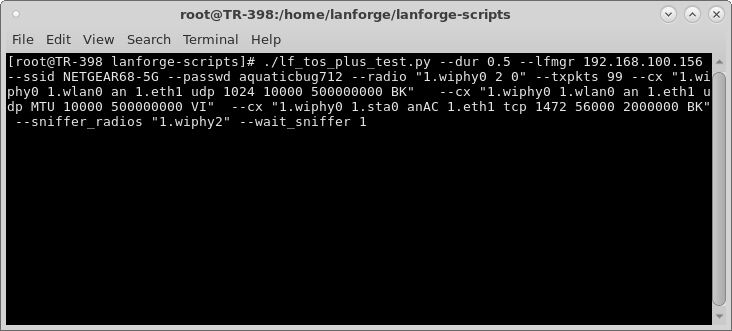
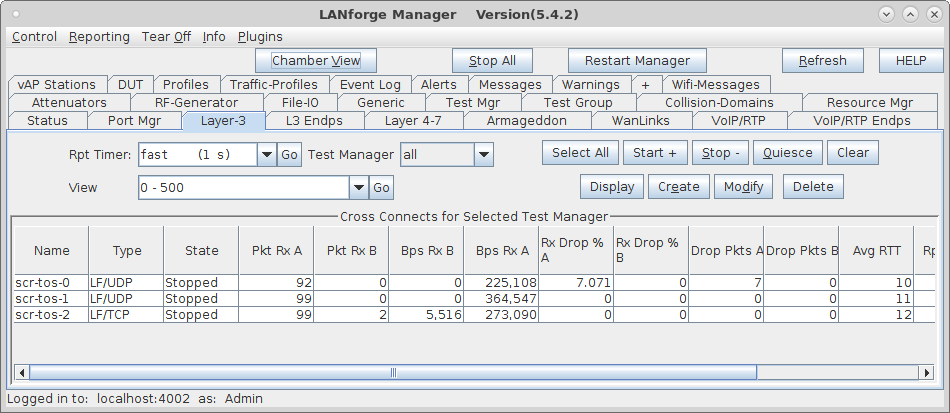
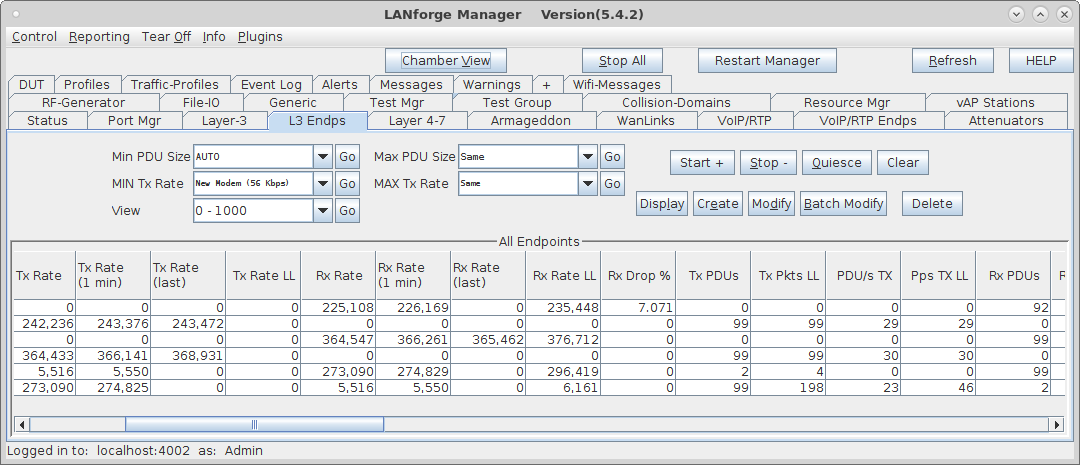
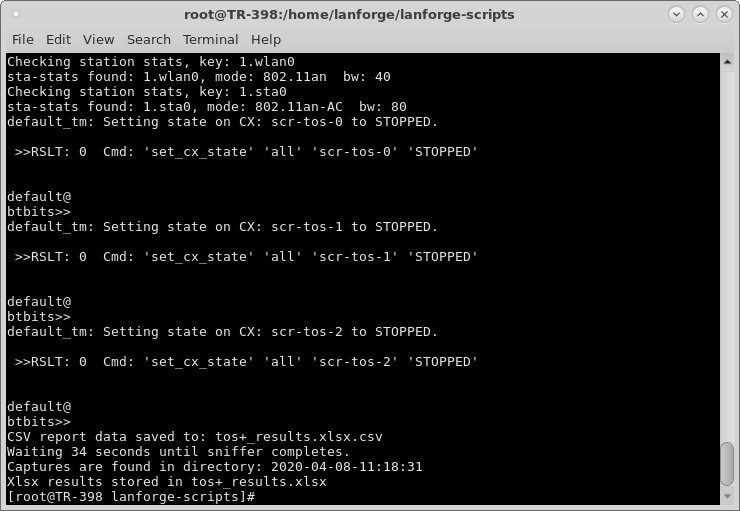
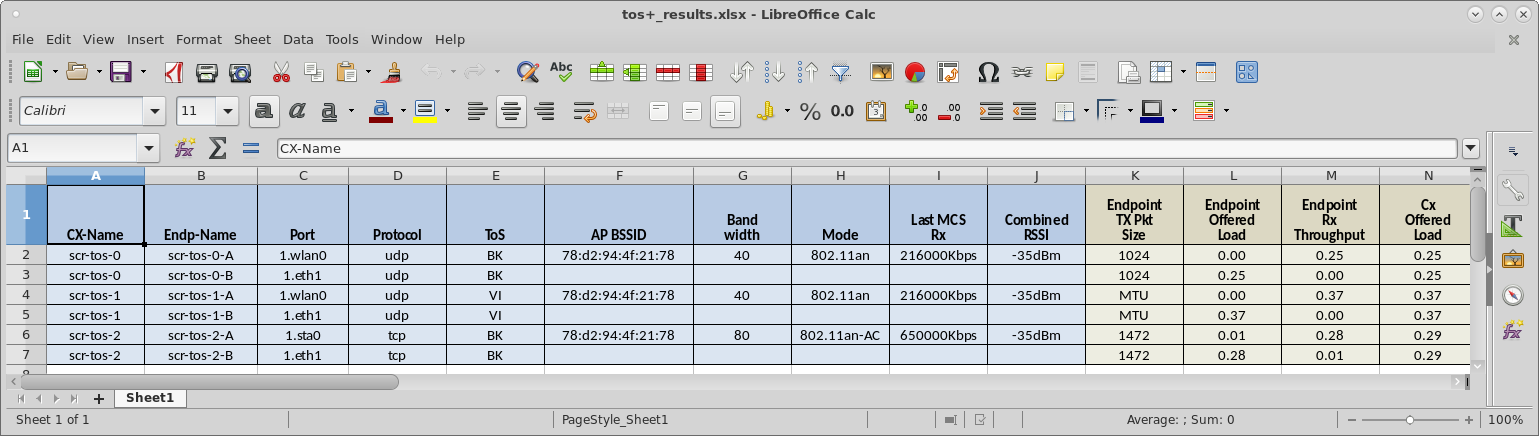
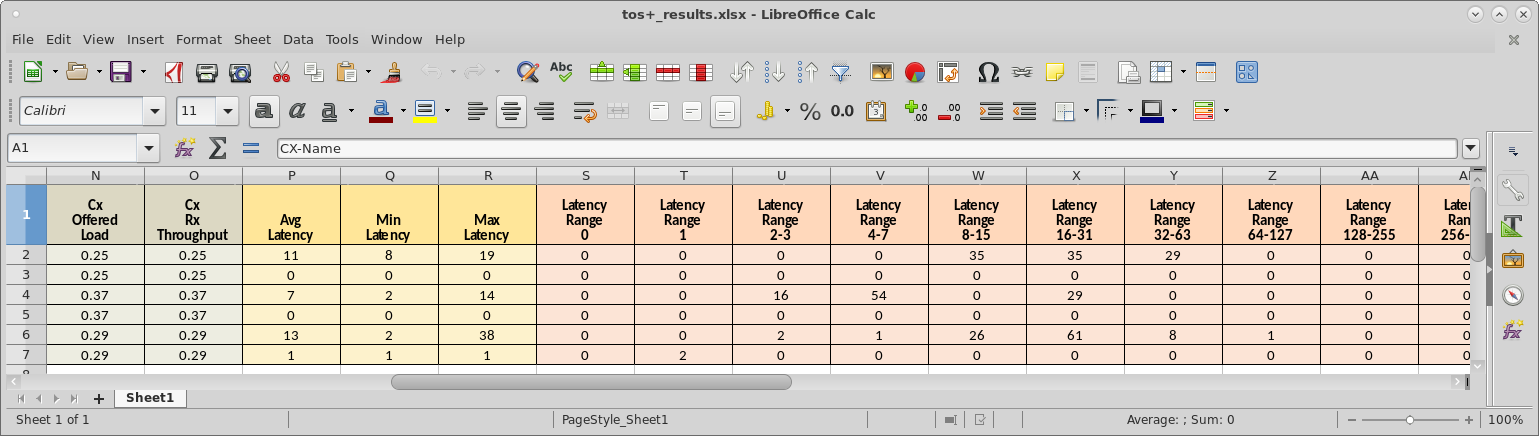
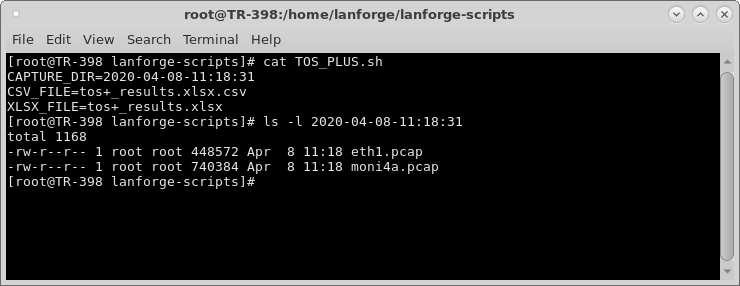
This script automates creating data connections with BK, BE, VI, VO and/or other QoS settings, as well as packet sizes, protocol type, and offered load. It then starts packet captures on the Ethernet port and RF monitor interfaces. The traffic and packet captures run for a specified amount of time and XLSX and CSV reports are generated to report latency and throughput. The packet captures are placed into a directory for post-processing by user-supplied tools. This script requires LANforge 5.4.2 or higher.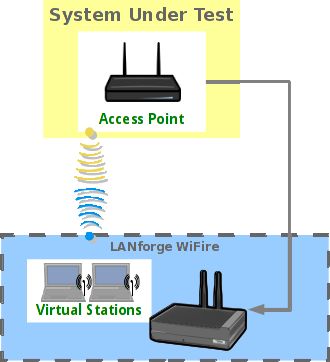 |
|